Webinar
Think About Your Audience Before Choosing a Webinar Title
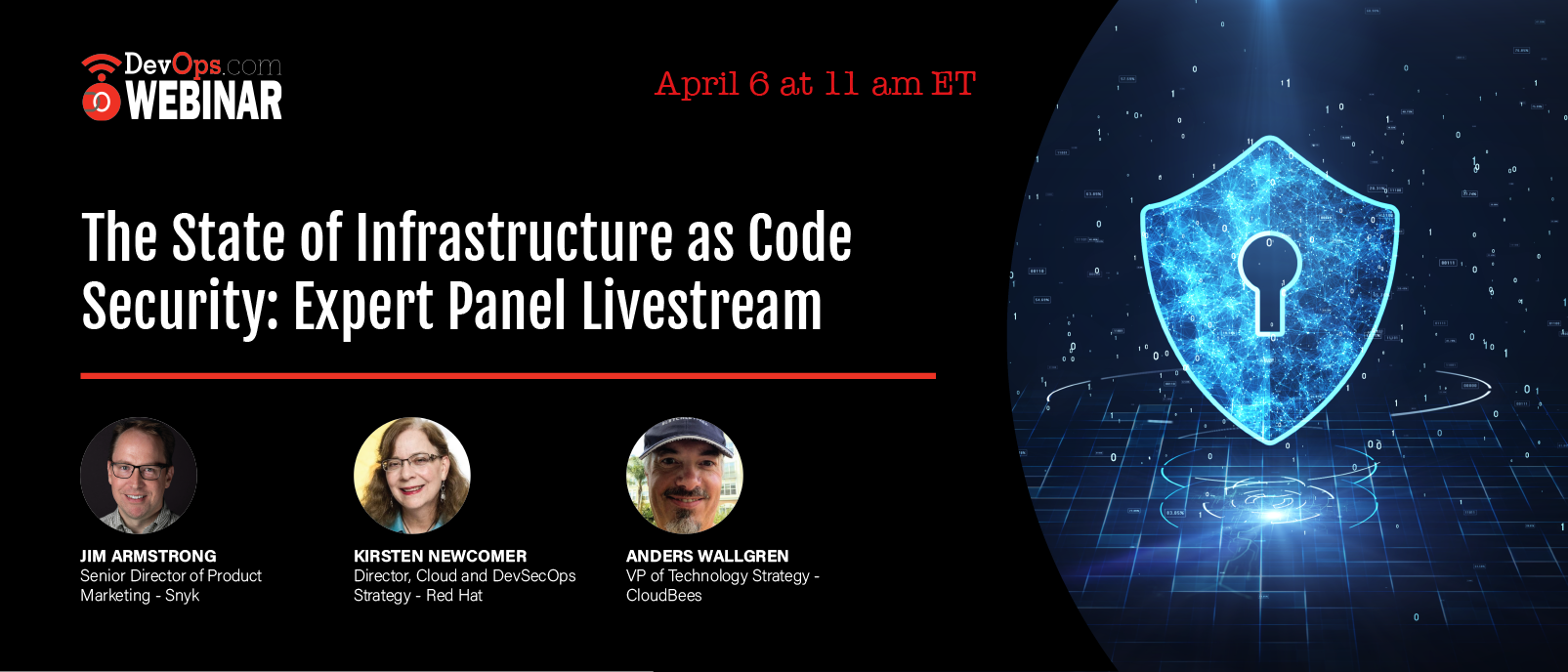
Sponsored by snyk, cloudbees & Red Hat
What You’ll Learn in This Webinar
The adoption of infrastructure-as-code and configuration-as-code is soaring with the rising popularity of technologies like Kubernetes and Terraform. This means that designing and deploying infrastructure is a developer task, even if your “developer” is an infrastructure architect, and, just like application code, configurations can use test-driven methodologies to automate security prior to deployment.
But how many companies actually do automate and test all their configurations before deployment? And does it really make a difference when problems do occur? Snyk recently conducted a survey to gauge how organizations are adopting IaC technologies -- and more importantly, securing them.
Join this livestream on April 6th at 11am ET with Snyk and experts on automated software delivery and Kubernetes from CloudBees and Red Hat, as they share never before seen findings and discuss security best practices along the way. Topics of discussion include:
- security testing throughout the CI pipeline,
- misconfiguration trends,
- IaC remediation patterns, and more.
Have a question you want to get answered during the livestream? Submit any questions and we’ll be sure to cover it: Submit questions







