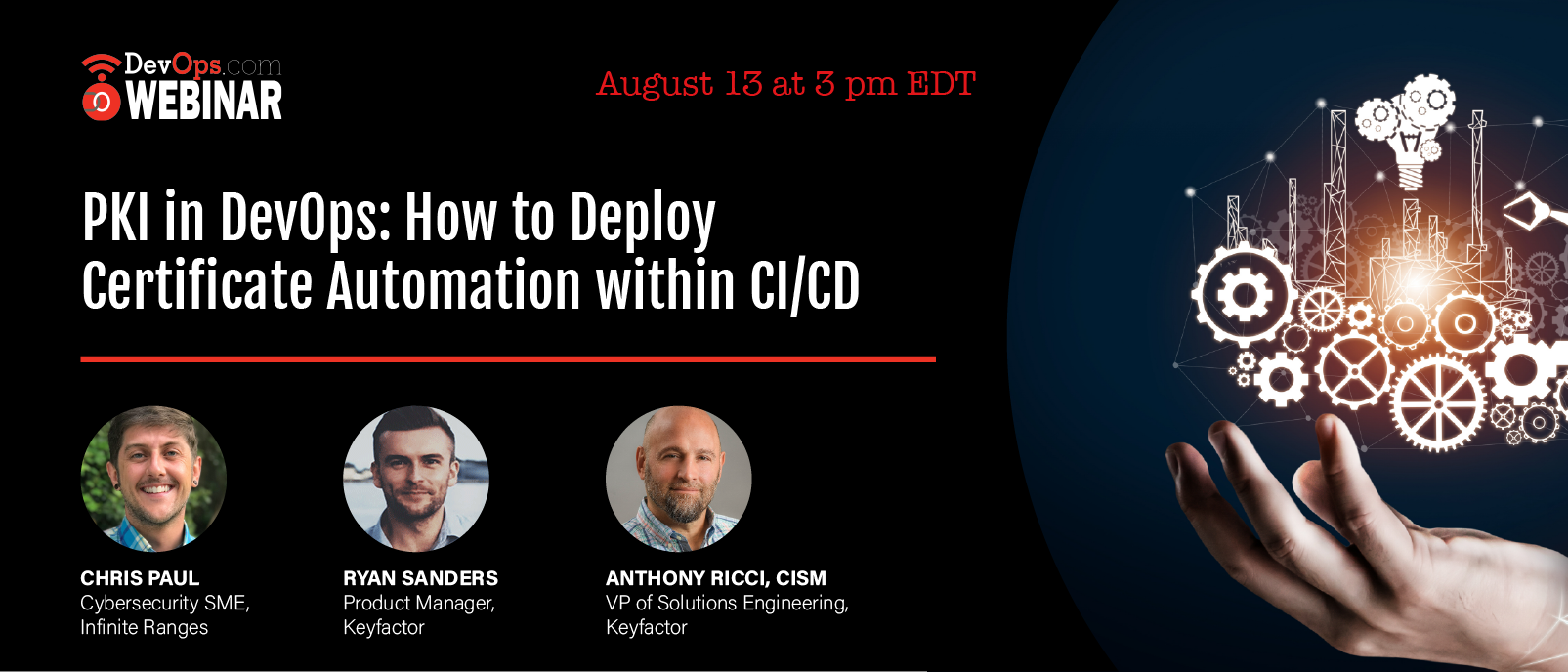
PKI in DevOps: How to Deploy Certificate Automation within CI/CD
Webinar
Think About Your Audience Before Choosing a Webinar Title
Sponsored by KEYFACTOR
Thursday, August 13, 2020
3 pm ET
What You’ll Learn in This Webinar
DevOps and CI/CD make for faster code releases, but they also create new challenges for security practices. Think about TLS and code-signing certificates. Almost every component in CI/CD – binaries, builds, web servers and containers – needs certificates to authenticate and verify trust, but traditional PKI processes just can't scale in DevOps environments.
Join Keyfactor and Infinite Ranges to learn how PKI and certificate management fits within the CI/CD pipeline and why an integrated and automated approach is key to success. In this webinar, we'll discuss:
- How applications in the DevOps toolchain use PKI (i.e. Jenkins, Kubernetes, Istio, etc.)
- The risks of unmanaged or untracked certificates in DevOps environments
- Best practices to support visibility, compliance and automation of certificates in CI/CD
Anthony Ricci, CISM
VP of Solutions Engineering - Keyfactor
A business-savvy technology leader, Anthony’s nearly 30 years of IT expertise has allowed him to grow and develop into an essential leader for Keyfactor. Drawing on a career history of results bridging business and technology to develop world-class IT solutions, Anthony has lead numerous enterprise IT initiatives for mid-size to Fortune 500 organizations alike. In his current role at Keyfactor, he is responsible for managing the entire solutions engineering team, focused on fostering individual SE growth and creating a positive technical experience for prospects as well as current customers.
RYAN SANDERS
Product Manager - Keyfactor
As a Product Manager at Keyfactor, Ryan has a passion for cybersecurity and actively analyzes the latest in compliance mandates, market trends, and industry best practices related to public key infrastructure (PKI) and digital certificates. More recently he has specialized in code signing fundamentals and security best practices to prevent software supply chain attacks. Prior to joining Keyfactor, he held product-related roles at a Toronto-based data encryption and key management solutions provider.
CHRIS PAUL
Cybersecurity SME - Infinite Ranges
Chris is prior Military Intelligence Systems Maintainer/Integrator, Cyber Network Warfare Specialist and Certified Endpoint Exploitation Analyst. A solutions-focused professional and subject matter expert with over 13 years of diverse experience working in the cybersecurity National Defense Industrial Complex as well as e-banking/online-insurance, community tech-startups, DevOps and DevSecOps spaces. As a Cyber Course Developer, experienced in world traveling as a Computer Network Exploitation and Defense Instructor for the U.S. State Department, he has authored many courses to be taught at the National Cryptologic School. Such as Introduction to Adversary Tactics – Red Team Threat Emulation, and follow on courses including IoT Pentesting Foundations and ICS/SCADA Penetration Techniques. When not doing that he is a devoted husband and father to two sons, chocolate labradoodle, and can be found eating tacos and playing drums.







