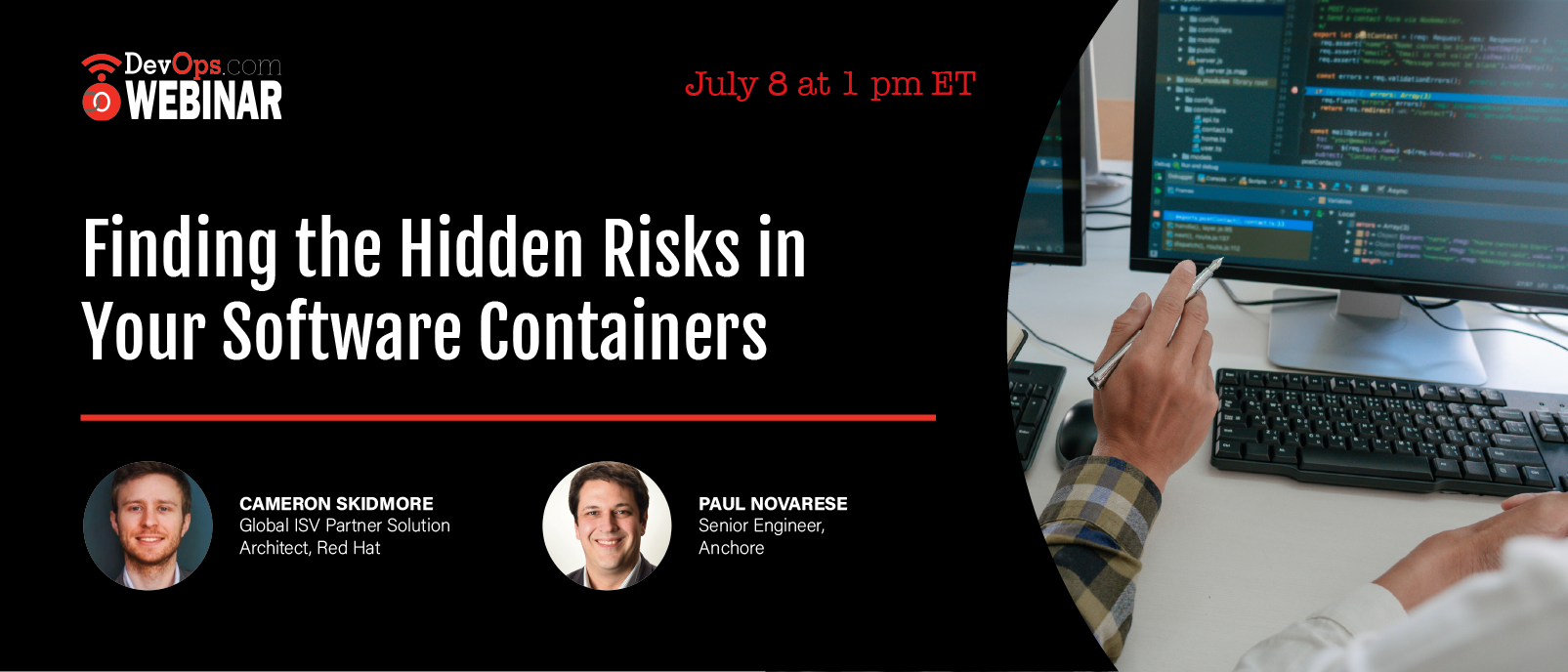
Finding the Hidden Risks in Your Software Containers
Webinar
Think About Your Audience Before Choosing a Webinar Title
Sponsored by RED HAT
Thursday, July 8, 2021
1 p.m. ET
What You’ll Learn in This Webinar
Software applications today include components from many sources, including open source, commercial components, and proprietary code. As software supply chain attacks have increased recently--including Codecov, Solar Winds, and others--organizations must embed security and compliance checks in every step of their software development process.
In this webinar, you will learn how to secure your software supply chain for containerized applications, including:
- Understanding possible attack points in the software supply chain
- How containers introduce risk the software supply chain
- The secrets, malware, and configuration risks that could be hiding in your software containers--and what do about it
- Best practices for securing containers at every stage of the process
Cameron Skidmore
Global ISV Partner Solution Architect - Red Hat
Cameron Skidmore is a Global ISV Partner Solution Architect. He has experience in enterprise networking, communications, and infrastructure design. He started his career in Cisco networking, later moving into cloud infrastructure technology. He now works as the Ecosystem Solution Architect for the Infrastructure and Automation team at Red Hat.
Paul Novarese
Senior Engineer - Anchore
Paul has been working in open source software for over 20 years, providing technical support, training, and general consulting, with a specialization in containers and cloud computing for over six years.







