DevOps Security, Monitoring and Compliance with OpenShift and Sysdig
Webinar
Think About Your Audience Before Choosing a Webinar Title
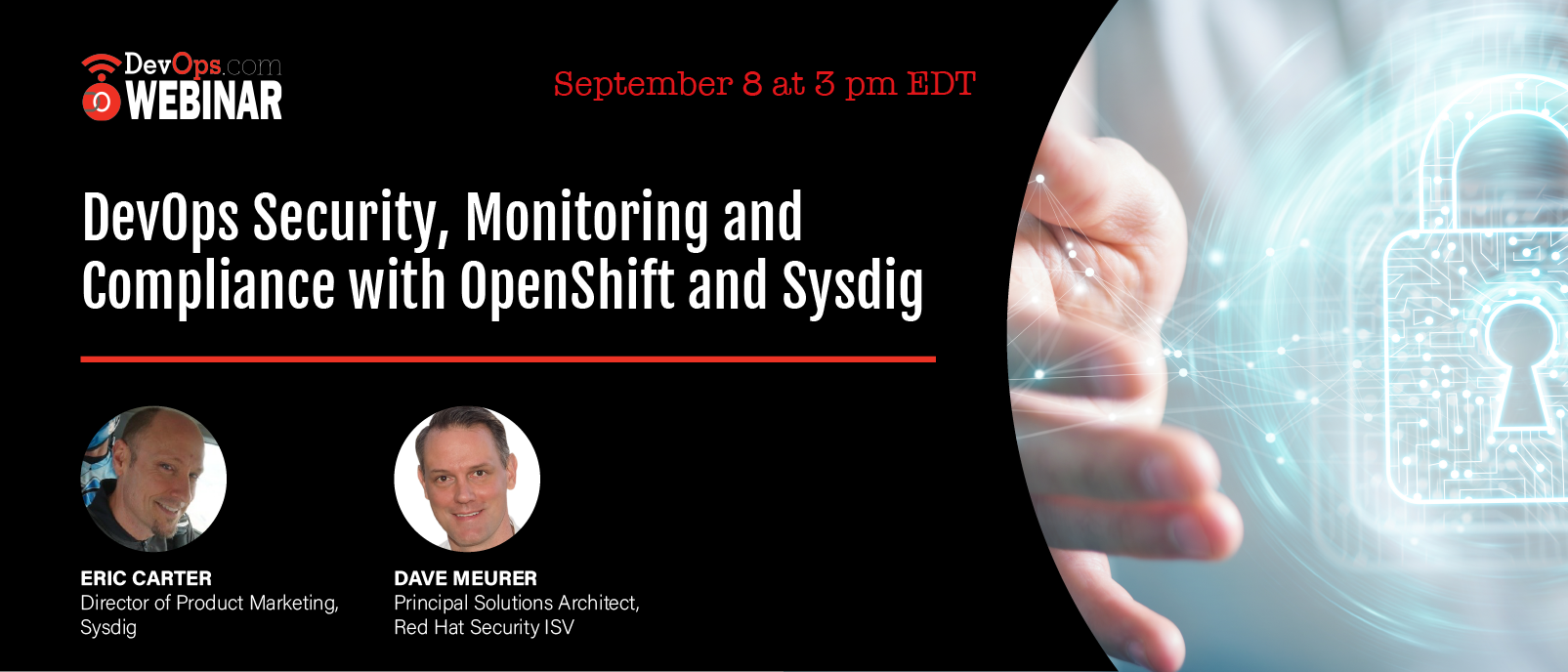
Sponsored by SYSDIG
Tuesday, September 8, 2020
3 pm EDT
What You’ll Learn in This Webinar
Ensuring application security and compliance is one of the biggest challenges for any organization deploying applications in production. You need to detect and block vulnerabilities, quickly respond to incidents, and meet compliance standards and policies. With Red Hat and Sysdig, your DevOps workflow transforms into a secure DevOps workflow. In this session, you’ll hear about the Falco open source project, customer examples and use cases for deploying Sysdig & Red Hat OpenShift, and see a real-world demo for securing your OpenShift environment without disrupting application deployments.
Join us to see how to:
- Integrate vulnerability management across your CI/CD pipeline
- Manage regulatory compliance, audit, and risk
- Define security policies for detecting and blocking threats in real time
- Maintain visibility into containerized apps for reliable performance and operations
Dave Meurer
Principal Solutions Architect - Red Hat Security ISV
Dave Meurer currently serves as a Principal Solution Architect on the Red Hat Global Partner Security ISV team, where he owns technical relationships and evangelism with security independent software vendor partners of Red Hat. Before joining Red Hat, Dave spent 9 years in the Application Security industry with Synopsys and Black Duck, where he served in similar roles as the director of technical alliances and sales engineering. Dave also worked for Skyway Software, HSN.com, and Accenture in various management and application development roles. When he’s not thinking about k8s, security, and partners, he enjoys being the VP Sales of North Central Tampa for his wife (the CEO) and 5 kids (Inside Sales). Follow him on LinkedIn and Twitter at @davemeurer. He mostly just posts pictures of homemade pizza.
Eric Carter
Director of Product Marketing - Sysdig
Eric is Director of Product Marketing at Sysdig focused on monitoring, alerting, troubleshooting and security solutions for containers and microservices. He’s been helping enterprises optimize and accelerate systems and applications for more than two decades. Prior to joining Sysdig, Eric led product marketing and management for the software-defined storage startup, Hedvig, and has held sales and product roles at Riverbed, EMC, and Legato Systems. Eric holds a BA in Public Relations from Pepperdine University.







